Firewall Protection and its various nuances you should know

All PCs and IT devices use a firewall to protect the device from malicious attacks and content. It acts like a guardian that protects your device from all the foreign attacks.
Today we will discuss the various nuances related to a firewall such as
-
What is firewall protection?
-
What are the three types of firewalls?
-
What does a firewall do and how does a firewall work?
-
Does the firewall protect against hackers?
Let us get started!
What is firewall protection?
Associating PCs with other IT frameworks or the web opens up a scope of positive potential outcomes — a simple coordinated effort with others, joining of assets, upgraded innovativeness — yet it likewise opens clients to threats.
Hacking, data fraud, malware, and online misrepresentation are regular dangers clients could confront when they uncover themselves by connecting their PCs to a system or the web.
Imagine a scenario where there was a way clients could shield themselves from the extremely most exceedingly awful perils by raising an undetectable divider to sift through those dangers. It is fundamental to have it — luckily, it as of now exists. That undetectable divider is what is known as a firewall.
Raised between a PC and its association with an outside system or the web, a firewall chooses which system traffic is permitted to go through and which traffic is considered hazardous. It basically attempts to sift through the great from the awful, the trusted from the untrusted.
A firewall is a bit of equipment or programming that anticipates malware and malignant assaults from entering a PC or a system of PCs through the Internet. The name firewall originates from this present reality security that keeps the fire from infiltrating past that point. Firewalls are basic boundaries between joined carports and a house, and between a car motor and the traveler compartment.
The across the board utilization of firewalls starts after the principal realized Internet worm, the Morris worm. What was expected to be a genuine test by an understudy to perceive what number of PCs were joined to the Internet, the Morris worm wound up causing enormous forswearing of-administration assaults? Appraisals of the harm caused the worm extend from $10 million to $100 million, however it additionally demonstrated that Internet specialist co-ops at the time were not set up for the projection of such an assault.
What are the 3 Types of Firewalls?
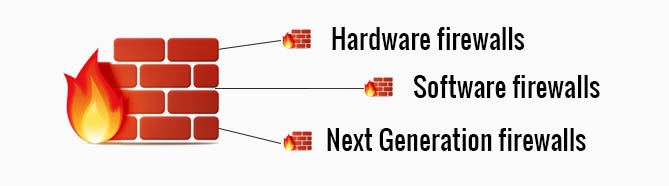
Hardware firewalls
Typical hardware firewalls are frameworks that are free of the PCs they ensure that channel the Internet as data goes into a PC. Most broadband Internet switches have their own firewall inherent.
By and large, equipment firewalls work by analyzing the information that streams in from the Internet and confirming whether that data is protected. Basic firewalls, known as parcel channels, inspect the information itself for data, for example, its area and its source.
At that point, the data the firewall assembles is contrasted with a set rundown of authorizations so as to decide if the data ought to be dropped or permitted through. As equipment firewalls have gotten further developed, they have picked up the capacity to look at more data.
These kinds of firewalls have their advantages for home and independent ventures since they expect practically no set-up, and numerous hubs (PCs) can be shielded from fixing into a similar switch.
Nonetheless, the significant downside to common home-use hardware firewalls is the way that they just look at the information that is coming in to a PC, and not the information leaving a PC. An individual may ask, "Isn't that the point?" In a way, yes. Yet, as a rule, malevolent programming is sent through the Internet masked in a Trojan steed.
The "wrapping" of the information may appear to seem to originate from a dependable source, yet imbedded into the coding might be the harming programming. Likewise, a few assaults may end in the objective PC turning into a zombie or a PC bot, which at that point starts to communicate information on a terrific scale. Since an equipment firewall doesn't recognize the active data, it won't think about the ascent in rush hour gridlock or its substance.
Software firewalls
There are two principal focal points that product firewalls have over equipment ones. The first is that product firewalls can screen active information traffic. In addition to the fact that this prevents a PC from turning into a bot or a zombie, yet additionally it can keep PCs from broadcasting some other malware, for example, worms or PC infections.
The other bit of leeway is that product firewalls are adaptable. These projects can be changed in accordance with address the issues of the client, for example, if they need consents to be facilitated up while they're internet gaming or viewing an online video.
In any case, the primary inconvenience to programming firewalls is that they just secure one PC. Each PC must have its very own authorized firewall item. Then again, an equipment firewall can secure each PC appended to it.
Next Generation firewalls
Advancing dangers keep on requesting increasingly extraordinary arrangements, and cutting-edge firewalls remain over this issue by consolidating the highlights of a conventional firewall with organize interruption aversion frameworks.
Truth be told, risk explicit cutting-edge firewalls are intended to analyze and distinguish explicit threats, for example, progressed malware, at an increasingly granular level. All the more every now and again utilized by organizations and modern systems, they give an all-encompassing answer for sifting through risks.
What does a firewall do and how does a firewall work?
Firewalls utilize one or a blend of the accompanying three strategies to control traffic streaming all through the system:

-
Packet filtering
The most fundamental type of firewall programming utilizes pre-decided security rules to make channels – if an approaching bundle of data (little lump of information) is hailed by the channels, it isn't permitted through. Bundles that endure the channels are sent to the mentioning framework and all others are disposed of.
-
Proxy service
A firewall intermediary server is an application that goes about as a mediator between frameworks. Data from the web is recovered by the firewall and afterward sent to the mentioning framework and the other way around. Firewall intermediary servers work at the application layer of the firewall, where the two parts of the bargains are compelled to lead the session through the intermediary. They work by making and running a procedure on the firewall that mirrors a help as though it were running on the end host, and in this manner concentrate all data move for an action to the firewall for examining.
-
Stateful inspection
The most present-day technique for firewall filtering, that doesn't depend on the memory-serious assessment of all data parcels is 'stateful investigation'. A 'stateful' firewall holds critical traits of every association in a database of confided in data, for the term of the session. These characteristics, which are by and large known as the 'condition' of the association, may incorporate such subtleties as the IP locations and ports engaged with the association and the grouping quantities of the bundles being moved. The firewall thinks about data being moved to the duplicate applicable to that move held in the database – if the examination yields a positive match the data is permitted through, else it is denied.
What firewalls do? Does it protect against Hackers?
A firewall is a framework intended to avoid unapproved access to or from a private PC arrange. Firewalls are much of the time used to keep unapproved Internet clients from getting to private systems associated with the Internet (regularly depicted as intranets).
All messages entering or leaving the intranet go through the firewall, which looks at each message and hinders those that don't meet the predetermined security criteria.
You need a firewall to shield your secret data from those not approved to get to it and to ensure against vindictive clients and mishaps that begin outside your system.
One of the most significant components of a firewall is its entrance control highlights, which recognize great and terrible traffic.
There are different sorts of firewall. In climbing request, they are
* Packet layer : This examinations organize traffic at the vehicle convention layer.
* Circuit level : This approves bundles are either association or information parcels.
* Application layer : This guarantees legitimate information at the application level before associating.
* Proxy server : This blocks all messages entering or leaving the system.
In reality, dangers have advanced throughout the years and firewalls have developed to manage them. While it is as yet conceivable to purchase parcel just firewalls, they are not sufficient for business use.
Assurance against blend dangers is best given by firewalls which consolidate the entirety of the above components.
Explicit capacities performed by firewalls include:
* Gateway barrier
* Carrying out characterized security arrangements
Conclusion
This is all we have in-store today! Keep reading our blogs to know more about various aspects of technology and hardware.
Let us know if you have any queries or doubts related to anything here. We will be happy to resolve it.















Comments (0)